Smart, automated, ASAP dissemination of security vulnerability updates to WoG!
Our team conducted user research, including in-depth interviews with five users. Since our team comprise problem owners, we had direct business insights throughout the process. This dual perspective allowed us to align our solution closely with both user needs and operational requirements.
Key insights from our research include:
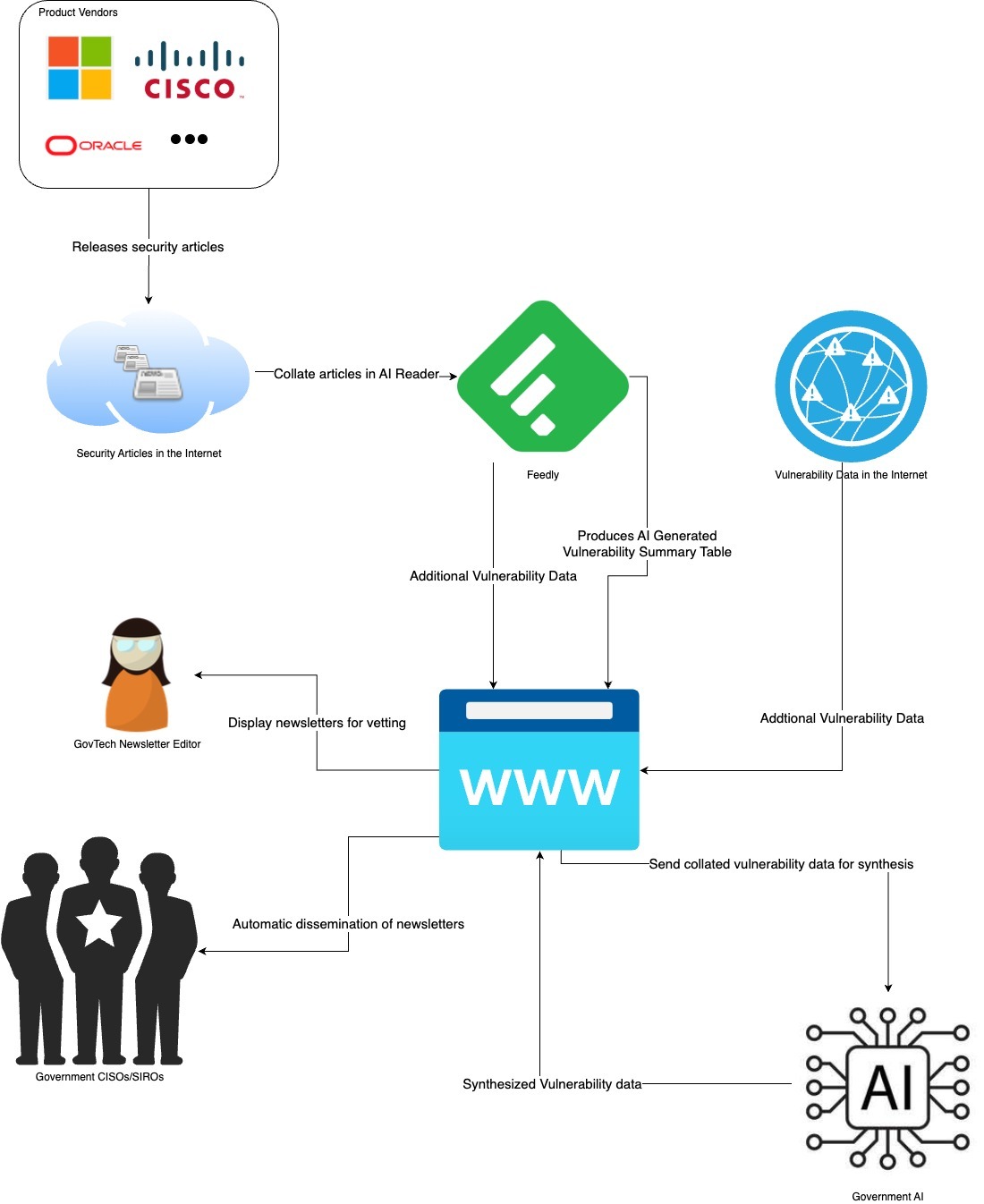
Smart and automated solution to enable timely and remediation of vulnerabilities across WOG. We believe that leveraging on AI and automation will hasten the process and reduce human errors in generating and dissemination of security vulnerability information.
Through our market research, we identified as a tool that can help to support in the process of collating security vulnerability information and thus decided to adopt and enhance it to better fit our requirements.
The Feedly solution will automate the scrapping of security vulnerability information from the internet. Thereafter the CVE metadata and AI-generated insights will be consolidated into newsletter format for review. Once approved, the newsletter will be disseminated to a pre-defined mailing list.